Update: Patched kernels are now in production
2026-05-01 21:07 UTC — The patched kernels are now rolling out to production repositories/mirrors. You no longer need to enable the testing repo to get them. Just run:
sudo dnf clean metadata && sudo dnf upgrade
sudo reboot
Most mirrors have a sync frequency of 3 hours. If the updates are not available to you yet we recommend trying again in about an hour.
The testing-repo instructions further down in this post remain for reference but are no longer the recommended path.
The kernels released to production repositories are bit for bit identical to those from testing. We’d like to thank everyone who helped with testing - it was the best involvement we’ve had for a community call for testing to date and contributed to the speed of getting these patches into production repositories!
Errata is available for all three supported AlmaLinux versions:
- 8: https://errata.almalinux.org/8/ALSA-2026-A001.html
- 9: https://errata.almalinux.org/9/ALSA-2026-A002.html
- 10: https://errata.almalinux.org/10/ALSA-2026-A003.html
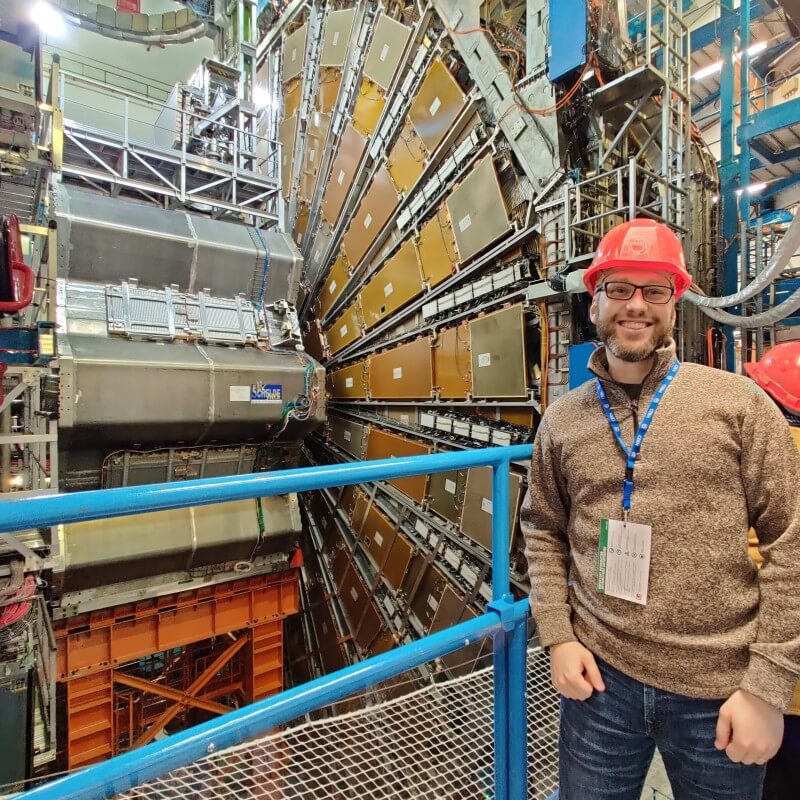
On April 29, the team at Xint Code disclosed a Linux kernel flaw they have named Copy Fail, tracked as CVE-2026-31431. The bug lives in the kernel’s crypto subsystem — a logic flaw in authencesn chained through AF_ALG and splice() — and it lets any unprivileged local user escalate to root with a 732-byte exploit that the researchers report works unmodified across every mainstream distribution built since 2017. Every supported AlmaLinux release is affected.
If you run AlmaLinux on a multi-tenant host, container build farm, CI runner, or any system where untrusted users can get a shell, this one matters.
More information about the vulnerability:
- https://copy.fail/
- https://xint.io/blog/copy-fail-linux-distributions
- https://github.com/theori-io/copy-fail-CVE-2026-31431
- https://nvd.nist.gov/vuln/detail/CVE-2026-31431
Patching ahead of our upstream
Security is a top priority at AlmaLinux, and the severity of this flaw — combined with how trivial it is to exploit — meant we did not want to wait. Patches are not yet available from Red Hat, so our core team has built patched kernels using the upstream fix (mainline commit a664bf3d603d, which reverts the 2017 optimization that introduced the bug). The decision to ship these ahead of a CentOS Stream / RHEL update was made by our technical steering committee, ALESCo.
These kernels are available in the testing repository today. After the community has helped verify them, we will release them to the production repositories. This blog post will be updated when that happens. Given the severity of this flaw, this update may hit production repositories over the weekend once we’re confident in the testing.
Help us test
It only takes a few steps to install and test the patched kernel from the testing repo.
Install the testing repo
sudo dnf install -y almalinux-release-testing
Update the kernel
sudo dnf update 'kernel*' --enablerepo=almalinux-testing
Reboot to load the new kernel
sudo reboot
Confirm you are running the patched kernel
The patched kernel versions are listed below. Use either of these commands:
uname -r
rpm -q kernel
We don’t recommend keeping the testing repo enabled after you’ve updated, unless you’ve done this on a truly non-production environment. If this is a production environment, you can disable the repo with this command:
sudo dnf config-manager --disable almalinux-testing
If you encounter problems, please let us know as soon as you can, either in AlmaLinux chat, on bugs.almalinux.org.
A note for AlmaLinux Kitten 10 users
AlmaLinux Kitten 10 is itself a development release and does not have a separate testing repository. The patched kernel is shipping directly to Kitten’s regular repository, so there is nothing extra to enable — just update and reboot:
sudo dnf update 'kernel*'
sudo reboot
Confirm with uname -r against the Kitten version listed below.
Patched kernel versions
- AlmaLinux 8 is patched in
kernel-4.18.0-553.121.1.el8_10and above - AlmaLinux 9 is patched in
kernel-5.14.0-611.49.2.el9_7and above - AlmaLinux 10 is patched in
kernel-6.12.0-124.52.2.el10_1and above - AlmaLinux Kitten 10 is patched in
kernel-6.12.0-225.el10and above
Thanks
Thanks to Brian Pak and the team at Xint Code for finding, responsibly disclosing, and writing up this vulnerability. His technical write-up is well worth reading if you want to understand how a single logic bug in authencesn becomes a fully reliable local privilege escalation.
Thanks to Andrew Lukoshko of the AlmaLinux core team for turning around patched builds for every supported release on disclosure day, and to ALESCo for moving quickly to approve shipping ahead of upstream. And thank you in advance to everyone in the community who helps us test these kernels — that’s the part that gets them safely into production.
Stay informed
Remaining aware of these vulnerabilities and acting quickly can keep your system and data safe. Follow the AlmaLinux Blog, join the Mattermost Community Chat, and subscribe to Announce and Security Mailing List to stay informed and updated. We will update this post when the patched kernels move from testing to production.
Changelog
2026-05-01 21:07 UTC — Patched kernels released to the AlmaLinux production repositories. Added a notice at the top of the post directing readers to
sudo dnf clean all && sudo dnf upgradeinstead of the testing-repo flow described below. Post title updated to reflect release.2026-05-01 16:30 UTC — Updated the kernel update command from
dnf update kerneltodnf update 'kernel*' --enablerepo=almalinux-testingso that all kernel-related packages (e.g.kernel-core,kernel-modules,kernel-headers) are updated together and if thealmalinux-testingrepo is already present but disabled, this will enable it for the transaction. This resolves an issue, unrelated to this patch, wherekernel-modules-extrais not upgraded when only upgradingkerneland an issue withalmalinux-testingbeing present but disabled so the instructions didn’t grab the updates. Also addedsudoto thednfcommands for consistency with therebootstep.